Enterprise design thinking cannot be properly defined without making reference to what it was built upon- the design thinking process. However, while both design thinking and enterprise design thinking share fundamental principles, methodologies, and objectives, they differ in scope, context, and application. Read on as we shed light on these distinct concepts.
Understanding Enterprise Design Thinking
As indicated by its name, enterprise design thinking concentrates on enterprises – large corporations, and intricate environments by utilising design thinking approaches. This involves more than just developing new products and services; it also involves developing new strategies, reorganising businesses, and changing corporate cultures. Enterprise Design Thinking is tailor-made for large corporations with complex and intertwined challenges. These challenges are broken down and approached using enterprise thinking processes, which will be discussed in the following section.
Process of Enterprise Design Thinking
The enterprise design thinking process is not a rigid framework but a flexible roadmap, designed to adapt to the unique needs and contexts of each enterprise endeavour.
Empathise
The process begins with empathy, which is like the core of the enterprise design thinking. This stage emphasises the significance of being aware of your users, comprehending their requirements, desires, and frustrations. It includes engaging with users through either verbal conversations or through observing their behaviour. This will assist businesses in obtaining the necessary information they require.
Define
Armed with empathy, the next step is to define the problem. In this phase, you distil your research findings into actionable insights, identify patterns, and articulate clear problem statements. By defining the scope and boundaries of the challenge, you lay the foundation for creative ideation and solution generation.
Ideate
Having a thorough grasp of the issue, now is the moment to let your imagination run wild. Ideation involves coming up with a variety of ideas, whether they are unconventional or realistic, without any criticism or limitations. It includes brainstorming meetings, sketching activities, and other innovative methods to examine different viewpoints and potential outcomes.
Prototype
Prototyping, is a method of bringing ideas into a tangible form, to determine their feasibility. Prototypes aim to quickly evaluate ideas, receive feedback, and improve solutions based on real observations, rather than focusing on achieving perfection.
Test
The last step in the process is to test the desired solution, where prototypes are given to users and stakeholders to receive feedback and validation. Testing is a continuous process that involves using insights from each round to make refinements and improvements to the solution. By accepting feedback and making iterations, you guarantee that your solutions are genuinely focused on the user and suitable for the intended purpose.
However, working together is crucial at every level. Multidisciplinary in nature, enterprise design thinking draws on a range of viewpoints and specialties, from those of designers and engineers to business executives and end users. Through the encouragement of collaboration, curiosity, and trial-and-error testing, firms may apply design thinking to tackle challenging issues, ignite innovation, and leave a lasting impact.
Implementing Enterprise Design Thinking
Introducing enterprise design thinking in a company goes beyond just embracing a new approach; it necessitates a significant change in attitude, culture, and behaviours. Outlined below are strategies for organisations to successfully implement enterprise design thinking.
- In implementing new organisational processes, various issues often reveal themselves. One of these issues is resistance to change. Enterprises must cultivate a culture that values creativity, empathy, and experimentation. They should foster open communication, risk-taking, and a willingness to accept new methodologies.
- Leaders must not only support enterprise design thinking but also promote its adoption and integration into current processes. It is necessary for them to assign resources, eliminate obstacles, and set a positive example by adopting a user-focused approach.
- Training and educational sessions to prepare staff with the necessary tools, skills, and mindset for successful enterprise design thinking should be ensured in organisations. Provide workshops, classes, and practical activities to develop design thinking skills throughout the company.
- Give importance to engaging users during the entire design process. Engage users and stakeholders in the early stages frequently to collaboratively develop solutions that align with their needs and preferences. Perform user research, test usability, and hold feedback sessions to confirm assumptions and make iterative design improvements
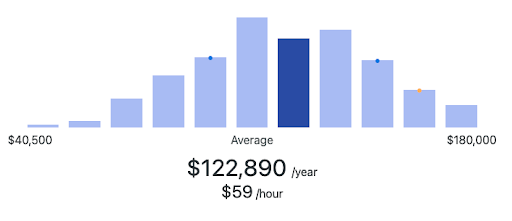
- Establish precise metrics and key performance indicators (KPIs) for assessing the effectiveness of enterprise design thinking efforts. Monitor advancement, collect input, and consistently adjust according to data-driven observations. Track results such as enhanced user happiness, boosted productivity, and company expansion.
Tools and Resources for Enterprise Design Thinking
In enterprise design thinking, having the appropriate instruments and resources at hand can significantly ease implementation and processes. Some of these tools include;
- Post-its – Post-its are sticker like coloured papers used to map and organise ideas. Every concept is written down on its own sticky note, and then organised into clusters based on similarities or themes. This procedure aids teams in recognising patterns, revelations, and possibilities, ultimately enhancing problem-solving and decision-making with greater precision.
- Five-whys – The five whys are a very effective technique for discovering the underlying cause of an issue. Change any issue into a question starting with “Why” – “Why is the issue occurring?” or “Why is the issue problematic?” Respond to that inquiry and construct it into a different “why” inquiry. Keep going until you finish asking the five whys, and hopefully, you will uncover the underlying issue. The objective is to identify the root causes of an issue rather than simply treating its surface symptoms.
- Personas – Personas are made-up individuals that are designed to embody various user categories, utilising information from actual users as a foundation. They are employed in design thinking and user-centred design methods to empathise with users, grasp their needs, motivations, and behaviours, and create products or services that fulfil their particular needs.
- Whiteboards – Whiteboards are useful tools for showcasing ideas, clarifying procedures, and giving interactive presentations. Using whiteboards allows presenters to quickly highlight key points, add notes to slides, and create diagrams, all of which enhance audience engagement and comprehension.
- Canva – With the help of Canva, users can work together to create a variety of visual content, including presentations, interfaces, posters, and much more, without the need for sophisticated design knowledge.
- Miro – Miro is a collaborative tool similar to Canva that aids in design creations, prototypes, and much more. Due to its simple methodology, even those without a great deal of experience can utilise it.
- Google Docs – Google Docs is an online word processing software that lets users create, edit, and collaborate on documents at the same time.